Jfrog Xray scanner reference
You can ingest scan results from JFrog Xray, a software composition analyis (SCA) solution that integrates with Artifactory and identifies vulnerabilities in open-source libraries and packages used in your code.
The standard workflow is to create a CI Build or Security Tests stage to your pipeline, add a Security step, and then use setting:value pairs to configure the step as specified below.
Before you begin
Harness STO supports
ingestionOnlyscans with Jfrog Xray.orchestrationOnlyanddataLoadscans are not supported.For information about running Xray scans with custom SSL certificates, go to Authenticating with RSA Keys in the JFrog documentation.
If you need to add trusted certificates to your scan images at runtime, you need to run the scan step with root access.
You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using self-signed certificates. For more information, go to Configure STO to Download Images from a Private Registry.
Security step settings
You can add a Security step to a Security Tests or CI Build stage and then configure it as described below.
Target and variant
The following settings are required for every Security step:
target_nameA user-defined label for the code repository, container, application, or configuration to scan.variantA user-defined label for the branch, tag, or other target variant to scan.
Make sure that you give unique, descriptive names for the target and variant. This makes navigating your scan results in the STO UI much easier.
You can see the target name, type, and variant in the Test Targets UI:
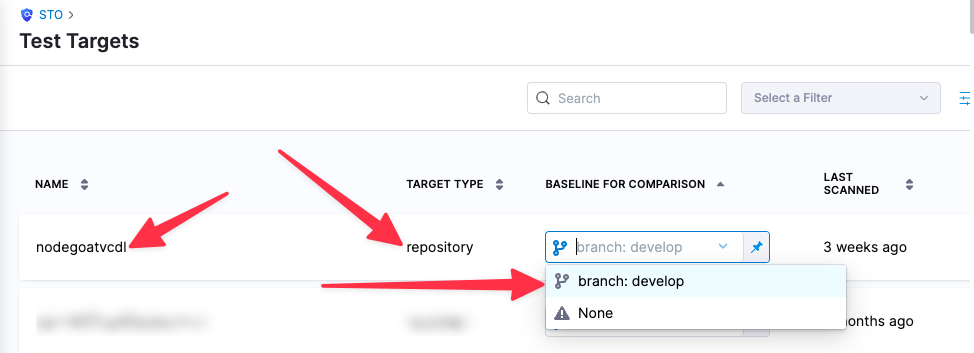
For more information, go to Targets, baselines, and variants in STO.
Jfrog Xray settings
product_name=xrayscan_type=containerImagepolicy_type=ingestionOnlyproduct_config_name=defaultfail_on_severity- See Fail on Severity.
Ingestion file
The following setting is required for Security steps where the policy_type is ingestionOnly.
ingestion_fileThe results data file to use when running an Ingestion scan. You should specify the full path to the data file in your workspace, such as/shared/customer_artifacts/my_scan_results.json.In addition to ingesting scan data in the external scanner's native format, STO steps can also ingest data in SARIF and Harness Custom JSON format.
The following steps outline the general workflow for ingesting scan data into your pipeline. For a complete workflow description and example, go to Ingest Scan Results into an STO Pipeline.
Specify a shared folder for your scan results, such as
/shared/customer_artifacts. You can do this in the Overview tab of the Security stage where you're ingesting your data.Create a Run step that copies your scan results to the shared folder. You can run your scan externally, before you run the build, or set up the Run step to run the scan and then copy the results.
Add a Security step after the Run step and add the
target name,variant, andingestion_filesettings as described above.
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none