CodeQL Scanner Reference
You can scan your code repositories using CodeQL, an analysis engine used by developers to automate security checks, and by security researchers to perform variant analysis.
The following steps outline the basic workflow:
Run a CodeQL scan, either externally or as part of a Run step, and publish the results to SARIF.
Add the SARIF data to your pipeline. If you ran the scan outside the pipeline, do the following:
In the stage where you ingest the results, go to Overview > Shared Paths and create a folder under
/sharedsuch as/shared/customer_artifacts.Use a Run step to add your scan results to the shared folder.
Use a CodeQL step to ingest the results.
This topic includes an end-to-end YAML pipeline that illustrates this workflow.
Before you begin
Root access requirements
You need to run the scan step with root access if you need to add trusted certificates to your scan images at runtime.
You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using self-signed certificates. For more information, go to Configure STO to Download Images from a Private Registry.
CodeQL step configuration
The recommended workflow is to add a CodeQL step to a Security Tests or CI Build stage and then configure it as described below. You can also configure CodeQL scans programmatically by copying, pasting, and editing the YAML definition.
- UI configuration support is currently limited to a subset of scanners. Extending UI support to additional scanners is on the Harness engineering roadmap.
- Each scanner template shows only the options that apply to a specific scan. If you're setting up a repository scan, for example, the UI won't show Container Image settings.
- Docker-in-Docker is not required for these steps unless you're scanning a container image. If you're scanning a repository using Bandit, for example, you don't need to set up a Background step running DinD.
- Support is currently limited to Kubernetes and Harness Cloud AMD64 build infrastructures only.
CodeQL Step Palette
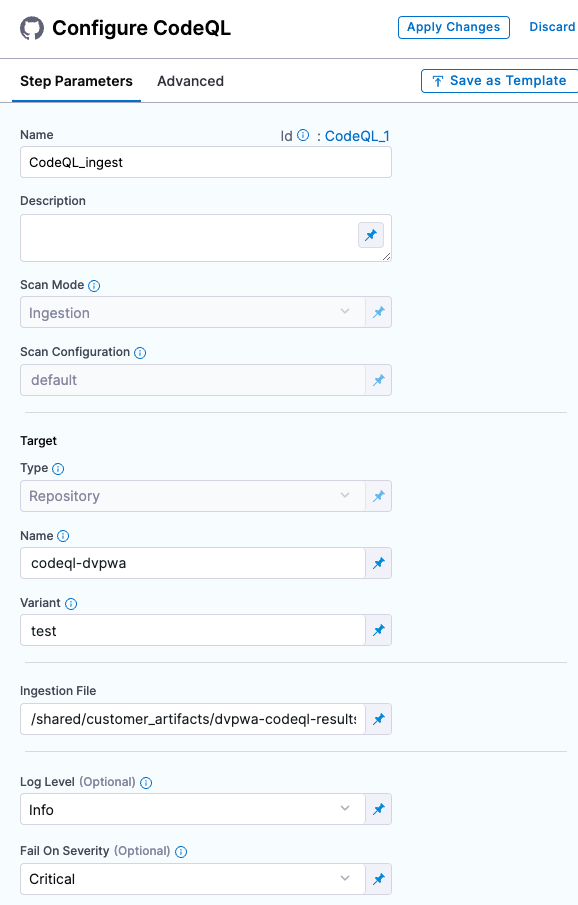
Scan Mode
- Ingestion Ingestion scans are not orchestrated. The Security step ingest results from a previous scan (for a scan run in an previous step) and then normallizes and compresses the results.
Scan Configuration
The predefined configuration to use for the scan. All scan steps have at least one configuration.
Target
Type
Repository Scan a codebase repo.
In most cases, you specify the codebase using a code repo connector that connects to the Git account or repository where your code is stored. For information, go to Create and configure a codebase.
Name
The Identifier that you want to assign to the target you’re scanning in the pipeline. Use a unique, descriptive name such as codebaseAlpha or jsmith/myalphaservice. Using descriptive target names will make it much easier to navigate your scan data in the STO UI.
Variant
An identifier for a specific variant to scan, such as the branch name or image tag. This identifier is used to differentiate or group results for a target. Harness maintains a historical trend for each variant.
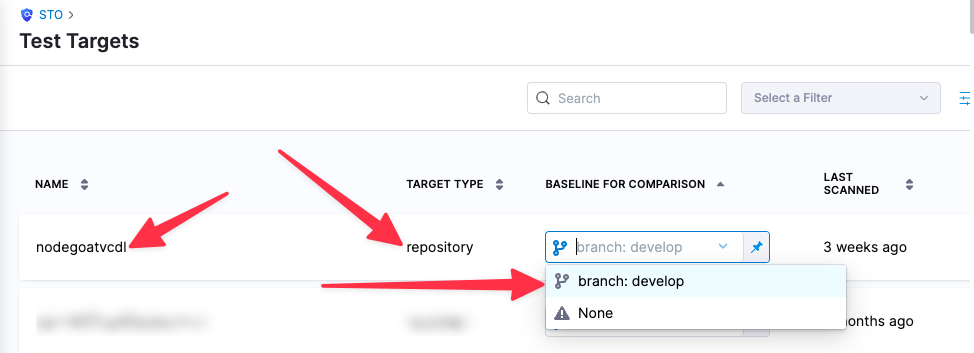
You can see the target name, type, and variant in the Test Targets UI:
Ingestion file
The results data file to use when running an Ingestion scan.
Generally an Ingestion scan consists of a scan step (to generate the data file) and an ingestion step (to ingest the data file).
In addition to ingesting scan data in the external scanner's native format, STO steps can also ingest data in SARIF and Harness Custom JSON format.
For more information, go to Ingest Scan Results into an STO Pipeline.
Log Level, CLI flags, and Fail on Severity
Log Level
The minimum severity of the messages you want to include in your scan logs. You can specify one of the following:
- DEBUG
- INFO
- WARNING
- ERROR
Additional CLI flags
You can use this field to customize the scan with specific command-line arguments supported by that scanner.
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none
Settings
You can add a tool_args setting to run the CodeQL scanner binary with specific command-line arguments.
Additional Configuration
In the Additional Configuration settings, you can use the following options:
Advanced settings
In the Advanced settings, you can use the following options:
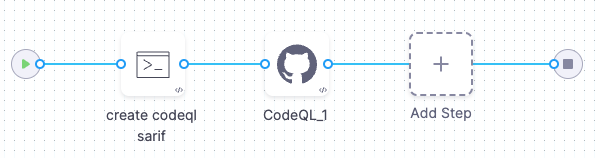
CodeQL pipeline example
The following pipeline example is an ingestion workflow. It consists of two steps. A Run step installs CodeQL, scans the repository defined in the Codebase object, and publishes the scan results to a SARIF file. A CodeQL step then ingests the SARIF file.
pipeline:
projectIdentifier: STO
orgIdentifier: default
tags: {}
stages:
- stage:
name: ingestion
identifier: ingestion
type: SecurityTests
spec:
cloneCodebase: false
infrastructure:
type: KubernetesDirect
spec:
connectorRef: my-harness-delegate
namespace: harness-delegate-ng
automountServiceAccountToken: true
nodeSelector: {}
os: Linux
execution:
steps:
- step:
type: Run
name: create codeql sarif
identifier: create_codeql_sarif
spec:
connectorRef: DockerHub
image: alpine
shell: Sh
command: |-
pwd
echo '{
"$schema": "",
"version": "sarif-2.1.0",
"runs": [
{
"tool": {
"driver": {
"name": "CodeQL",
"version": "2.5.7",
"semanticVersion": "2.5.7+1234567890",
"informationUri": "https://github.com/github/codeql",
"properties": {
"analysisTarget": "myproject",
"analysisTimestamp": "2023-04-03T14:00:00Z",
"analysisDuration": 120000,
"query": "detect-external-libs.ql",
"queryUrl": "https://github.com/github/codeql/blob/master/javascript/ql/src/semmle/javascript/Security/CWE/CWE-094/ExternalLibraries.ql"
}
}
},
"results": [
{
"ruleId": "js/detect-external-libs",
"message": {
"text": "The following external libraries were found: jQuery, Lodash"
},
"locations": [
{
"physicalLocation": {
"artifactLocation": {
"uri": "/path/to/myproject/js/script.js"
},
"region": {
"startLine": 10,
"startColumn": 1,
"endLine": 10,
"endColumn": 15
}
}
}
],
"level": "warning",
"properties": {
"severity": "high",
"confidence": "medium"
}
}
]
}
]
}'> codeql.sarif
ls
- step:
type: CodeQL
name: CodeQL_1
identifier: CodeQL_1
spec:
mode: ingestion
config: default
target:
name: login_microservice
type: repository
variant: my_hotfix_branch
advanced:
log:
level: info
fail_on_severity: critical
ingestion:
file: /harness/codeql.sarif
sharedPaths:
- /var/run
- /shared/customer_artifacts/
identifier: codeql_ingestion
name: codeql ingestion
The following YAML pipeline includes example stages for scanning a repository (Bandit step), an image (AquaTrivy step), and an app (ZAP step).
If you want to set up scan steps programmatically using YAML, the best practice is to set up your step in a pipeline using the Visual Editor and then copy, paste, and edit the YAML definition.
pipeline:
name: sto-step-palette-example
identifier: stosteppaletteexample
projectIdentifier: my_sto_project
orgIdentifier: default
tags: {}
properties:
ci:
codebase:
connectorRef: MY_GITHUB_CONNECTOR
build: <+input>
stages:
- stage:
name: runSecurityTestsStage
identifier: runSecurityTestsStage
type: SecurityTests
spec:
cloneCodebase: true
execution:
steps:
- step:
type: Background
name: docker_dind
identifier: Background_1
spec:
connectorRef: MY_DOCKER_CONNECTOR
image: docker:dind
shell: Sh
privileged: true
- step:
type: Bandit
name: banditScanRepo
identifier: banditScanRepo
spec:
mode: orchestration
config: default
target:
name: dvpwa
type: repository
variant: <+codebase.branch>
advanced:
log:
level: info
fail_on_severity: none
- step:
type: AquaTrivy
name: aquaTrivyScanContainerImage
identifier: aquaTrivyScanContainerImage
spec:
mode: orchestration
config: default
target:
name: myAlphaService
type: container
variant: latest
advanced:
log:
level: info
privileged: true
image:
type: docker_v2
name: jsmith/myalphaservice
domain: docker.io
tag: latest
- step:
type: Zap
name: zapScanInstance
identifier: zapScanInstance
spec:
mode: orchestration
config: default
target:
name: my-gruyere
type: instance
variant: test
advanced:
log:
level: info
instance:
domain: https://google-gruyere.appspot.com/XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX/
protocol: https
infrastructure:
type: KubernetesDirect
spec:
connectorRef: MY_K8S_CONNECTOR
namespace: harness-delegate-ng
automountServiceAccountToken: true
nodeSelector: {}
os: Linux
sharedPaths:
- /var/run